Enable SSO with OneLogin (OIDC)
Firezone supports Single Sign-On (SSO) using OneLogin through the generic OIDC connector. This guide will walk you through how to obtain the following config settings required for the integration:
- Config ID: The provider's config ID. (e.g.
onelogin) - Label: The button label text that shows up on your Firezone login screen.
(e.g.
OneLogin) - Scope:
OIDC scopes
to obtain from your OIDC provider. This should be set to
openid email profileto provide Firezone with the user's email in the returned claims. - Response type: Set to
code. - Client ID: The client ID of the application.
- Client secret: The client secret of the application.
- Discovery Document URI: The OpenID Connect provider configuration URI which returns a JSON document used to construct subsequent requests to this OIDC provider.
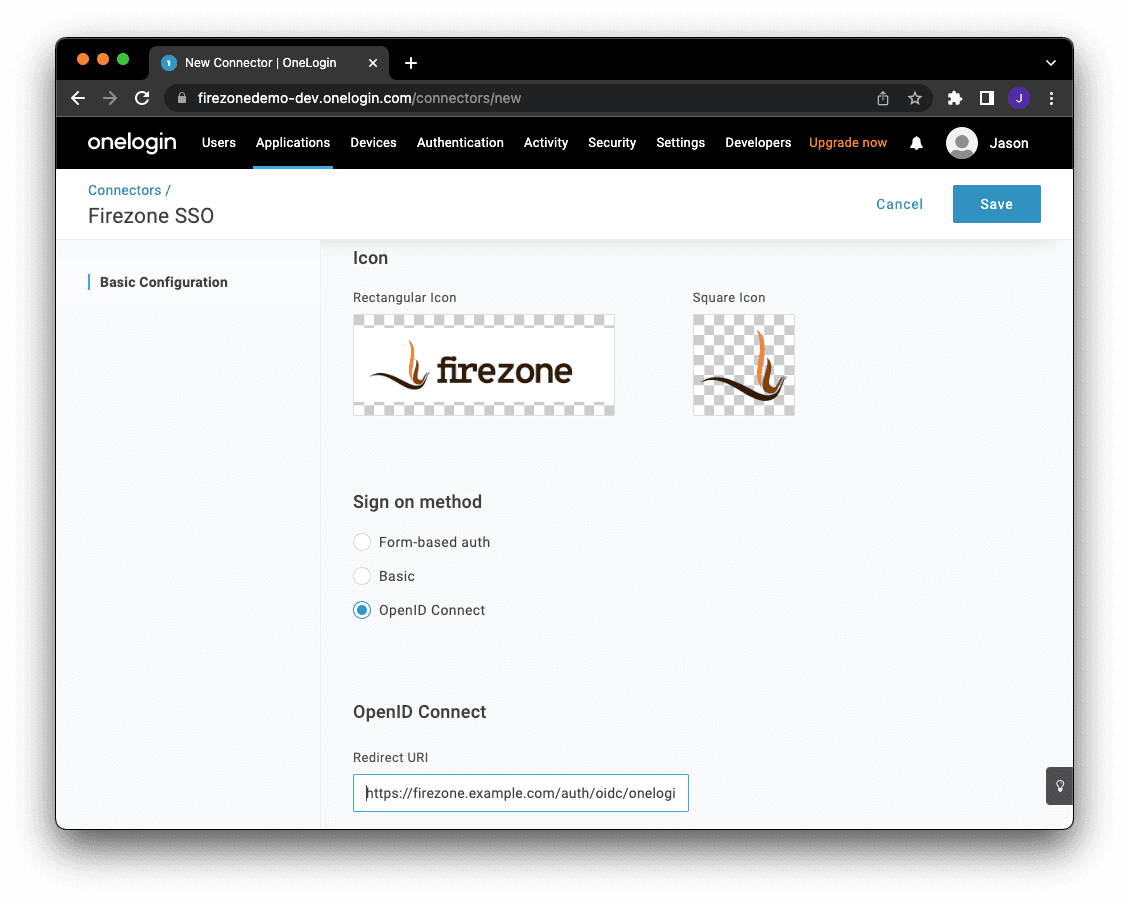
Step 1: Create custom connector
Create a new OIDC connector by visiting Appliances > Custom Connectors.
- App name:
Firezone - Icon: icon and logo.
- Sign on method: select OpenID Connect
- Redirect URI: Add your Firezone
<EXTERNAL_URL> + /auth/oidc/<Config ID>/callback/(e.g.https://firezone.example.com/auth/oidc/onelogin/callback/).
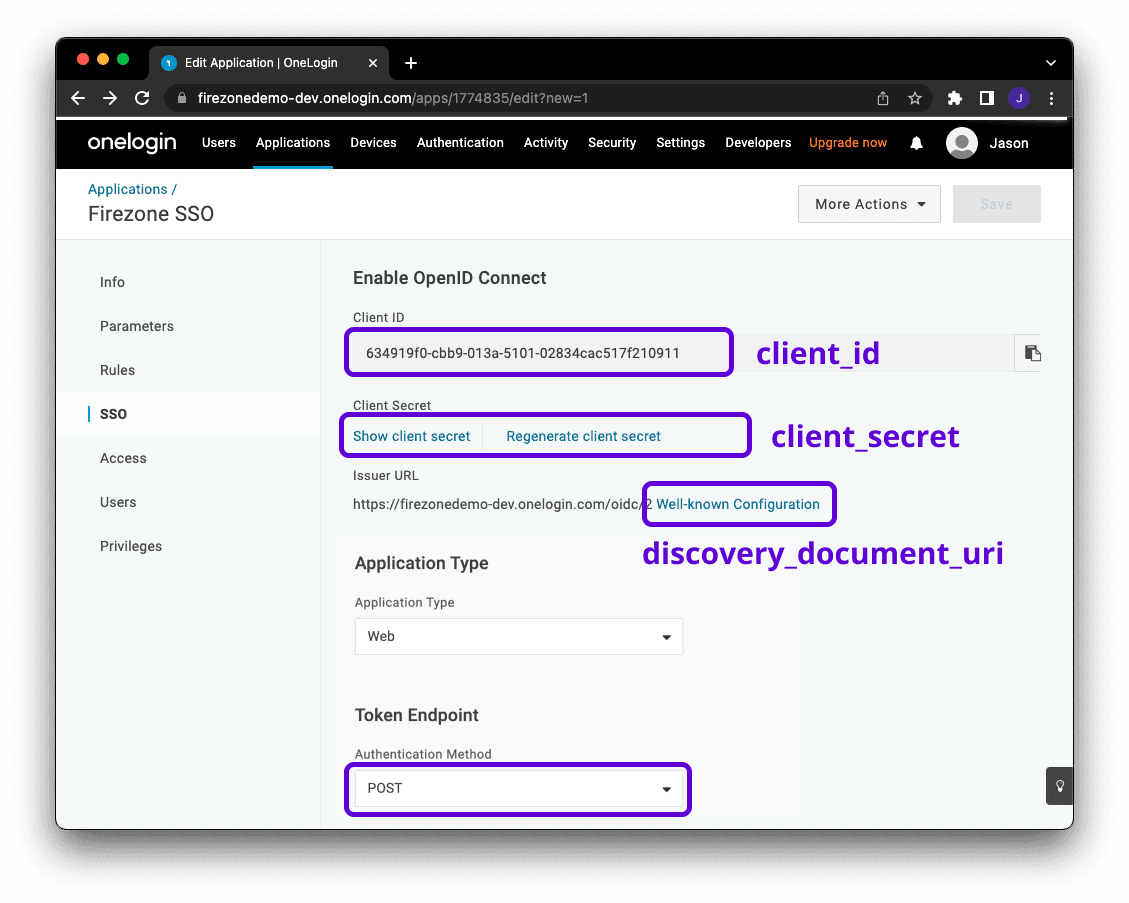
Step 2: Obtain configuration parameters
Next, click Add App to Connector to create an OIDC application. Visit the SSO tab, then change the token endpoint authentication method to POST.
You will find the values for the config settings required by Firezone on this page as well.
Step 3: Integrate with Firezone
Navigate to the /settings/security page in the admin portal, click "Add OpenID
Connect Provider" and enter the details you obtained in the steps above.
Enable or disable the Auto create users option to automatically create an unprivileged user when signing in via this authentication mechanism.
And that's it! The configuration should be updated immediately. You should now
see a Sign in with OneLogin button on the sign in page.